What is Phishing? What are the measures to avoid Phishing scam?
For nowadays computer users one of the greatest threats is the phishing attacks. It is one of the biggest challenges that the individuals and the companies face while securing their valuable data and prevent phishing and avoid the phishing scams. Hackers are nowadays relying most on it to exploit the users and get their personal details. Staying under the covers and attacking people from there has become one of the serious issues these days.
What is Phishing?
Knowing you’re are being tricked and scammed, avoid phishing scams, preventing phishing attacks so in a whole knowing what is phishing. Is all that phishing includes. There are some websites which provide the users with exclusive and catchy offers. Tries to trick the users into giving their usernames and passwords sometimes even the private information. This includes the websites such as the bank website, online shopping sites which are more into phishing.
The information which the Phishing site mainly asks are mentioned below:
- Passwords and Usernames.
- Account Number of your Banks.
- Social Security Numbers.
- Debit and Credit Card Numbers.
- Personal Identification Number.
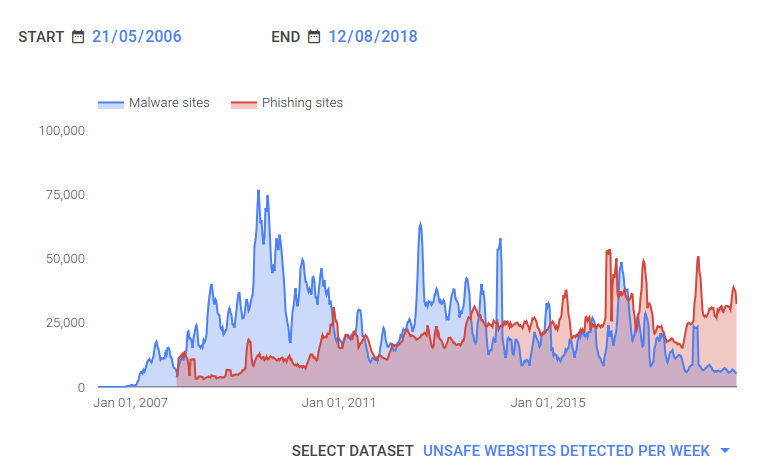
(source: google transparency report)
In digital media, Phishing has enlarged its hands in the form of phone calls and downloads from some anonymous websites. Excluding all this, the most common form of Phishing is through emails. In which the trickster possess to be a well-known company which you can trust easily. Later on, ask for your all private and valuable information.
These people Customize emails which contain the trusted company logos, font size etc is built for Phishing. Which makes the email more customized and trusted as it is from the original company. For example, the scammers claim that you have won a huge prize money and require your personal information for verification. Even sometimes ask to give feedbacks through which customers can win a prize for taking part.
Types of Phishing
- SPEAR PHISHING: It means the scammers just concentrate a specific people or group of people for phishing attempts. The tricksters may have sought the required information still in a hope of increasing the sources they have. However, it is one of the most successful phishing techniques on the internet until now.
- CLONE PHISHING: Whenever a lawful email is sent to the people the scammers take down the address from the links and attachment. After which they create a whole new and similar kind of email or a cloned email.
- WHALING: In this phishing type the scammers directly target the senior most persons of an organisation such as the CEO, CFO. Here, the emails and websites are more expertise and seriously at the executive level.
- VPHISING OR VOICE PHISHING: All the phishing techniques doesn’t necessary needs emails and websites. In this phishing type scammers call up and claim to call from banks and ask account numbers for verifications. They even, if use the fake caller id’s for making the fake calls more trusted.
HOW TO PREVENT PHISHING SCAMS?

Whenever you get a message from a website who is asking for your personal information. Before that Google pops-up, a message warning about the content is dangerous and deceptive. Below are some tips to avoid the Phishing scams:
- CLOSE THE DOORS FOR THREATS: To avoid Phishing the best and trusted way is to stay away from all those sites which are not trusted and you are going to use it for the first time. For email marketing try to avoid 99% of the unwanted emails which includes the dangerous links, deceptive attachments. Whenever Google warns about the malicious site its good to stop then and there. Web-filtering is also one of the important defence mechanism that helps in detecting the scam websites.
- SECURE YOUR PERSONAL INFORMATION: Always think before you click because the scammers don’t even leave a chance to spoof you. They can even attack you using simple things such as BEC or Business Email Comprise. Where we can’t find any links that are working or detect any of the attachments.
- CHECK THE EMAILS AND WEBSITE THOROUGHLY: Before jumping to a conclusion and giving all the details. If you get an email, addressing generically, having spelling and grammatical mistakes in the mail, and links redirecting to different sites then for sure these emails are from the hackers. These all are the next generation steps to stop spoofing.
- CHECK THE SOURCE: whenever you get an email from a bank always check the source of it. Because no bank will ever ask you to disclose the personal numbers, passwords, pin numbers etc. Try to avoid these kinds of emails if any doubt directly calls the bank and ask about it.
- INCREASE YOUR COMPUTER SECURITY: Having a good antivirus is the answer to this. Antivirus keeps your computer safe and secure from all the dangerous versions attacking your emails. And most importantly it even warns you about it. In addition to it, Antivirus gives the update about the present operating system and when to update it.